Secret Blizzard Deploys Malware in ISP-Level AitM Attacks on Moscow Embassies
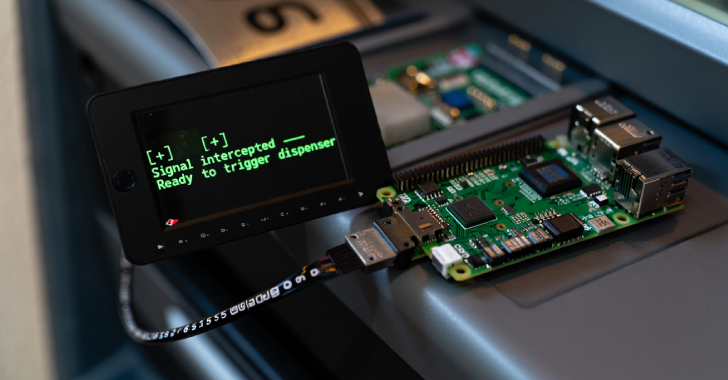
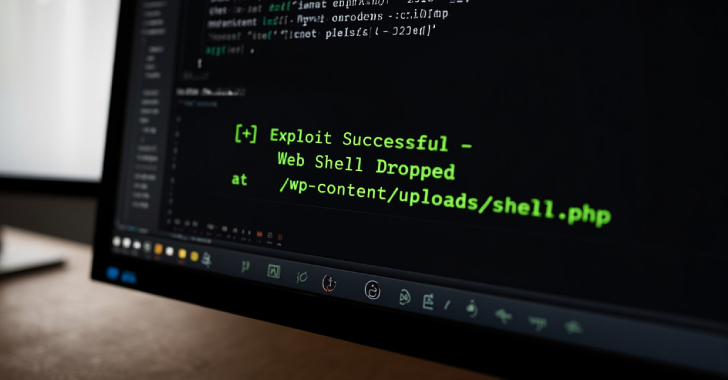
The Russian nation-state threat actor known as Secret Blizzard has been observed orchestrating a new cyber espionage campaign targeting foreign embassies located in Moscow by means of an adversary-in-the-middle (AitM) attack at the Internet Service Provider (ISP) level and delivering a custom malware dubbed ApolloShadow. “ApolloShadow has the capability to install a trusted root certificate […]
Cyber News