TP-Link Gaming Router Vulnerability Exposes Users to Remote Code Attacks
A maximum-severity security flaw has been disclosed in the TP-Link Archer C5400X gaming router that could lead to remote code execution on susceptible devices by sending specially crafted requests. The vulnerability, tracked as CVE-2024-5035, carries a CVSS score of 10.0. It impacts all versions of the router firmware including and prior to 1_1.1.6. It has […]
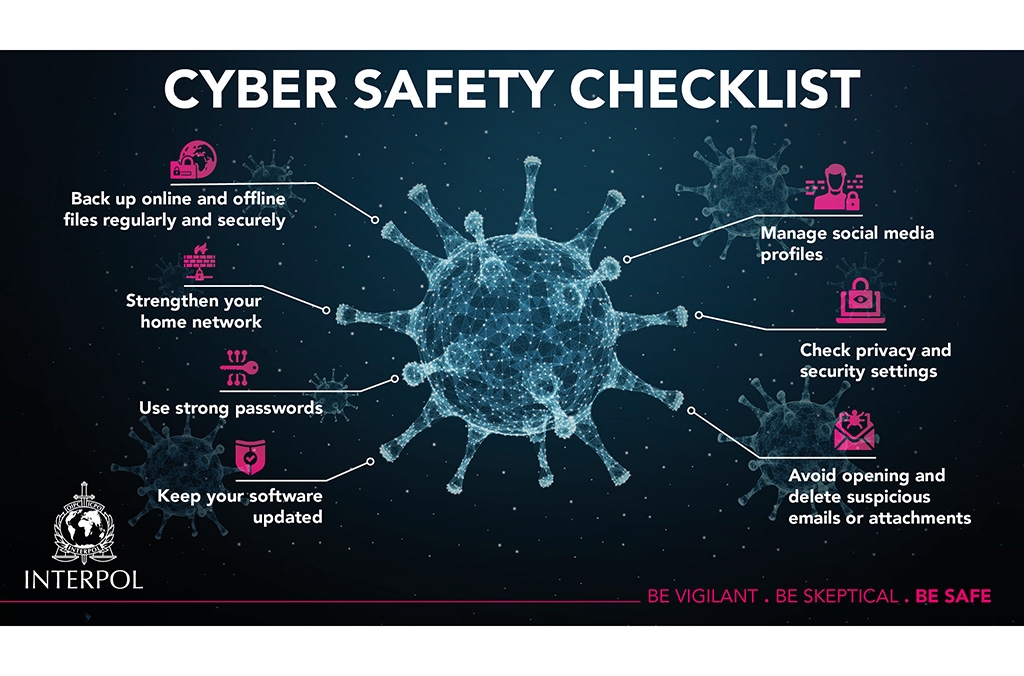
Cyber News