Cyber Espionage Alert: LilacSquid Targets IT, Energy, and Pharma Sectors
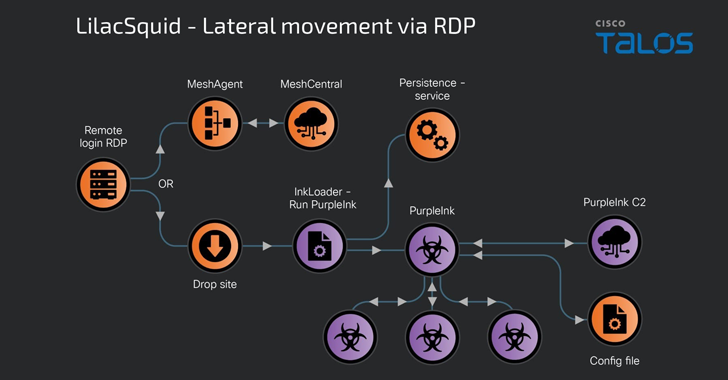
A previously undocumented cyber espionage-focused threat actor named LilacSquid has been linked to targeted attacks spanning various sectors in the United States (U.S.), Europe, and Asia as part of a data theft campaign since at least 2021. “The campaign is geared toward establishing long-term access to compromised victim organizations to enable LilacSquid to siphon data […]
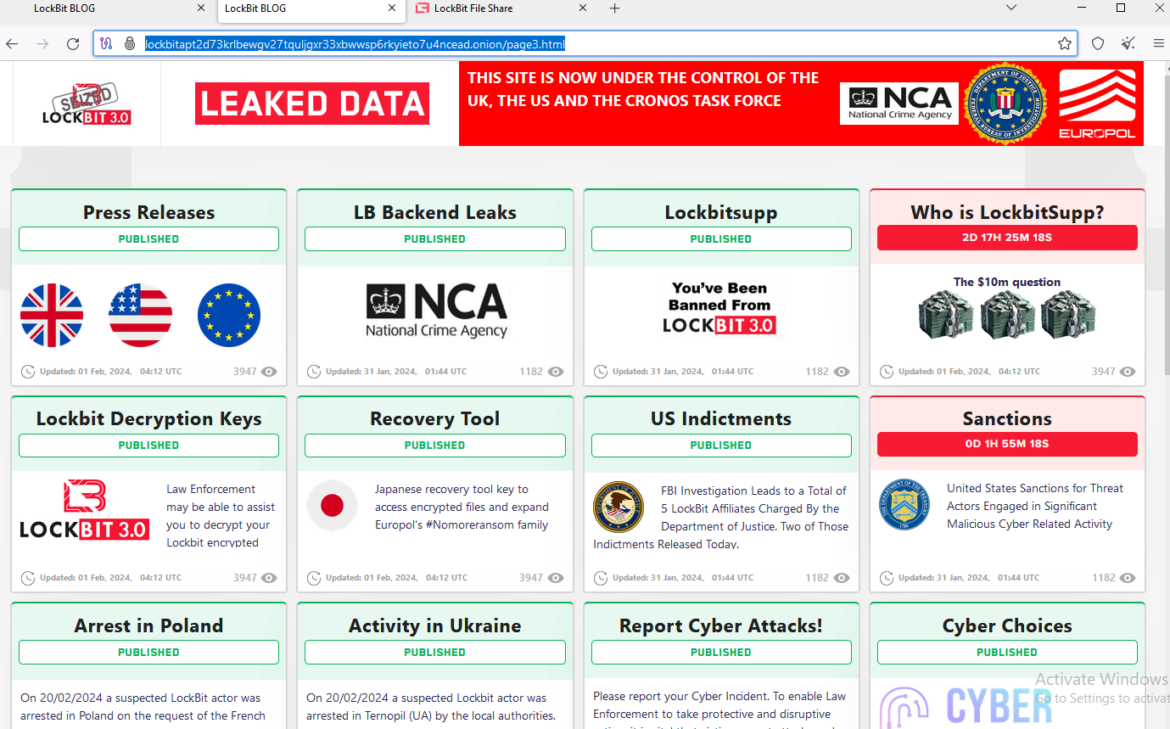
Cyber News