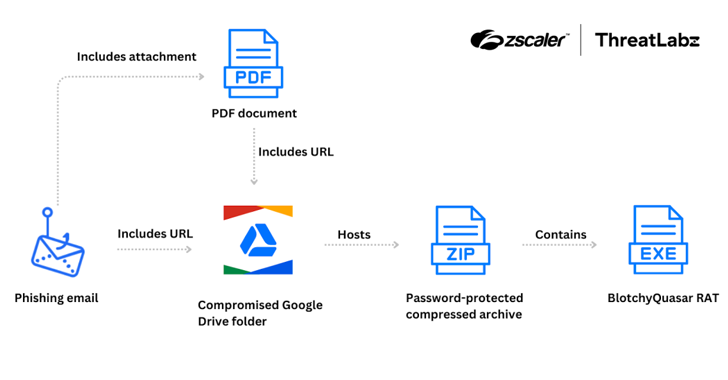
Blind Eagle Targets Colombian Insurance Sector with Customized Quasar RAT
The Colombian insurance sector is the target of a threat actor tracked as Blind Eagle with the end goal of delivering a customized version of a known commodity remote access trojan (RAT) referred to as Quasar RAT since June 2024. “Attacks have originated with phishing emails impersonating the Colombian tax authority,” Zscaler ThreatLabz researcher Gaetano […]
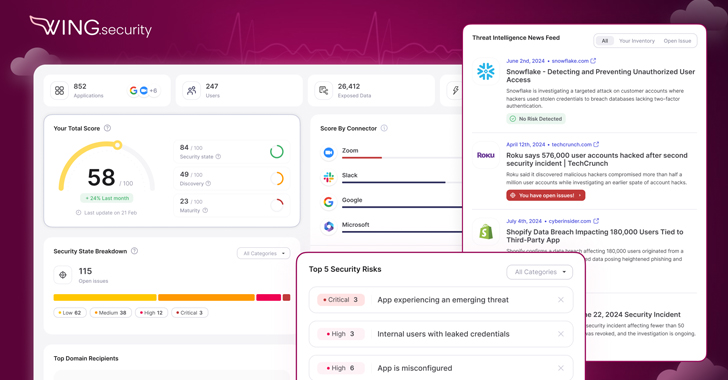
Cyber News