CosmicBeetle Deploys Custom ScRansom Ransomware, Partnering with RansomHub
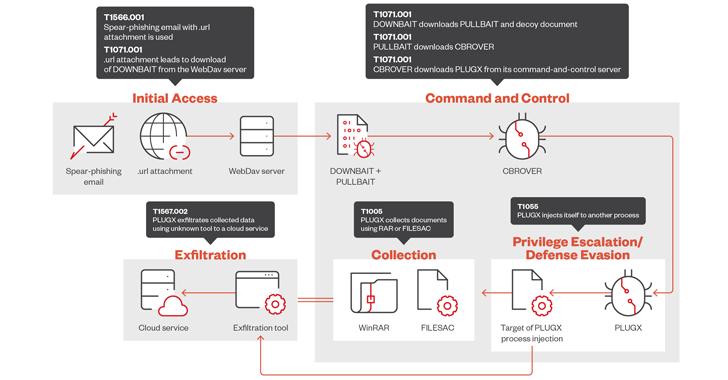
The threat actor known as CosmicBeetle has debuted a new custom ransomware strain called ScRansom in attacks targeting small- and medium-sized businesses (SMBs) in Europe, Asia, Africa, and South America, while also likely working as an affiliate for RansomHub. “CosmicBeetle replaced its previously deployed ransomware, Scarab, with ScRansom, which is continually improved,” ESET researcher Jakub […]
Cyber News