ToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft
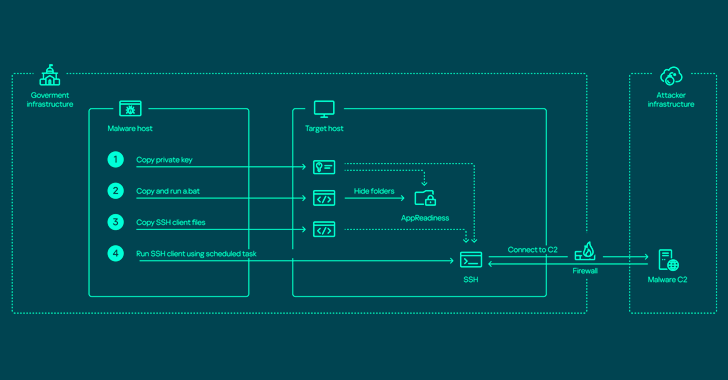
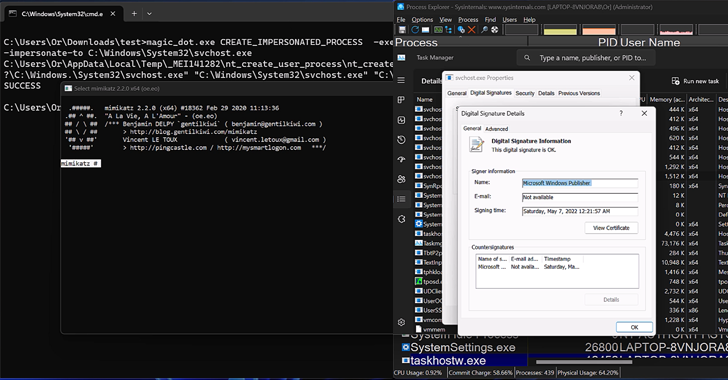
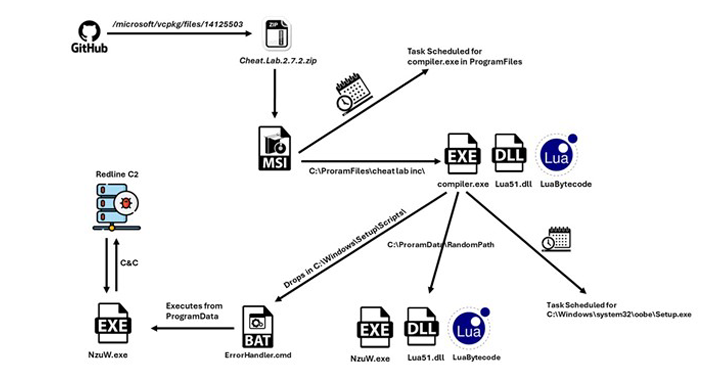
The threat actor known as ToddyCat has been observed using a wide range of tools to retain access to compromised environments and steal valuable data. Russian cybersecurity firm Kaspersky characterized the adversary as relying on various programs to harvest data on an “industrial scale” from primarily governmental organizations, some of them defense related, located in […]
Cyber News