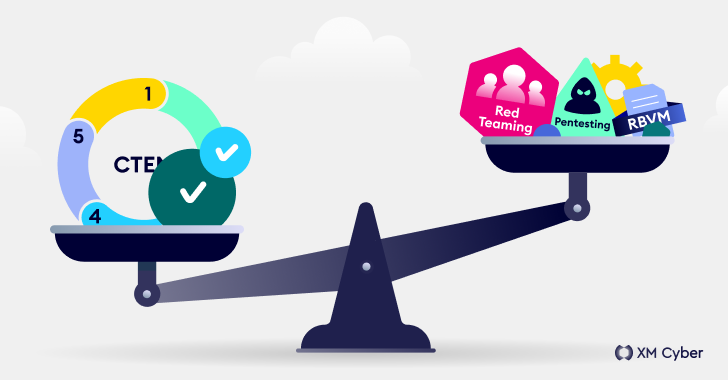
Navigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
It comes as no surprise that today’s cyber threats are orders of magnitude more complex than those of the past. And the ever-evolving tactics that attackers use demand the adoption of better, more holistic and consolidated ways to meet this non-stop challenge. Security teams constantly look for ways to reduce risk while improving security posture, […]
Cyber News