FedRAMP Shakes Things Up
Emergency Directive 25-03 and a Much-Needed Wake-Up Call
FedRAMP isn’t usually the life of the party. Predictable, methodical, steady—those are its moves. But this week? It threw not one, but two surprises on the table. And honestly, it’s about time.
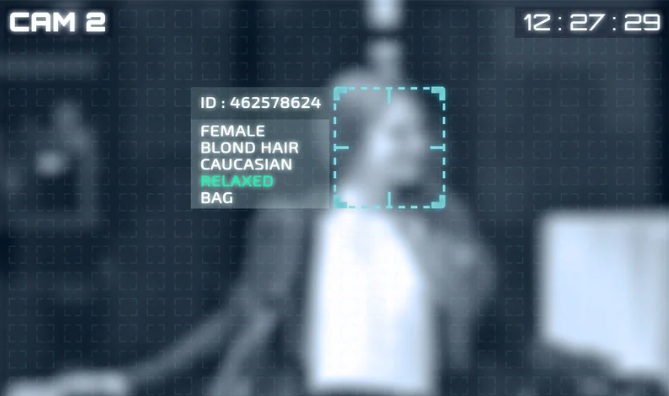
The catalyst was CISA’s Emergency Directive 25-03, a blunt reminder that communication during a crisis isn’t just nice to have—it’s life-or-death for cybersecurity. FedRAMP responded with a one-two punch: a routine reminder and a bold new requirement that could change the game.
Update #1: The Standard Play
First, FedRAMP issued a blog telling every Authorized provider to check their cloud service for affected devices, begin mitigation, and most importantly: talk to their customers. It’s classic incident response, nothing earth-shattering. But here’s the kicker: if you’re even a little unsure whether your team has done it, now is the time to ask.

Update #2: The Real Plot Twist
Here’s where it gets interesting. Alongside the directive, FedRAMP dropped RFC-0018, and the backstory says it all.
When FedRAMP blasted out an urgent, system-wide notification to every Authorized provider—the first in years—the results were, well… messy. We’re talking:
- Broken inboxes.
- Rejected emails.
- Providers burying messages behind portals.
In other words, critical emergency alerts weren’t always reaching the people who needed them. That’s not just an inconvenience. In a live-fire cyber emergency, it’s dangerous.
So FedRAMP’s new rule is simple, and honestly overdue: every security contact email will be tested quarterly. No more “we assumed you got it.” No more “it must’ve landed in someone’s spam folder.” This is FedRAMP saying: “When it matters most, we’re making sure the message actually gets through.”

Why This Matters
Let’s not sugarcoat it; this isn’t a burden, it’s a wake-up call. For too long, the soft underbelly of cloud security has been human failure: outdated contact info, neglected inboxes, and painfully slow communication chains. By validating those channels proactively, FedRAMP is elevating communication to the level of a critical control.
Frankly, it’s what should have happened years ago.
The Takeaway
If you’re a FedRAMP Authorized provider, here’s your action plan:
- Double-check your security contacts.
- Make sure your teams are actively monitoring those inboxes.
- Be prepared for the quarterly checks.
Because the next time an emergency directive drops, there won’t be room for a missed email.
Where Cyber Defense Advisors Comes In
At Cyber Defense Advisors (CDA), we help organizations turn these kinds of mandates into opportunities for resilience. FedRAMP’s new requirements aren’t just another box to check. They’re a chance to strengthen your incident response posture and prove to customers that you can be trusted when it matters most.
Whether it’s:
- Validating your FedRAMP security contacts and compliance workflows,
- Running tabletop exercises to stress-test communication in a crisis, or
- Building out broader strategies for CMMC, FedRAMP, or other compliance frameworks,
CDA is here to make sure your team doesn’t just “pass the test,” but thrives under pressure.







Leave feedback about this