A malware botnet called Ebury is estimated to have compromised 400,000 Linux servers since 2009, out of which more than 100,000 were still compromised as of late 2023.
The findings come from Slovak cybersecurity firm ESET, which characterized it as one of the most advanced server-side malware campaigns for financial gain.
“Ebury actors have been pursuing monetization activities […], including the spread of spam, web traffic redirections, and credential stealing,” security researcher Marc-Etienne M.Léveillé said in a deep dive analysis.
“[The] operators are also involved in cryptocurrency heists by using AitM and credit card stealing via network traffic eavesdropping, commonly known as server-side web skimming.”
Ebury was first documented over a decade ago as part of a campaign codenamed Operation Windigo that targeted Linux servers to deploy the malware, alongside other backdoors and scripts like Cdorked and Calfbot to redirect web traffic and send spam, respectively.
Subsequently, in August 2017, a Russian national named Maxim Senakh was sentenced to nearly four years in prison in the U.S. for his role in the development and maintenance of the botnet malware.
“Senakh and his co-conspirators used the Ebury botnet to generate and redirect internet traffic in furtherance of various click-fraud and spam email schemes, which fraudulently generated millions of dollars in revenue,” the U.S. Justice Department said at the time.
“As part of his plea, Senakh admitted that he supported the criminal enterprise by creating accounts with domain registrars that helped develop the Ebury botnet infrastructure and personally profited from traffic generated by the Ebury botnet.”
ESET’s investigation has unearthed various approaches the attackers use to deliver Ebury, including methods such as theft of SSH credentials, credential stuffing, infiltrating hosting provider infrastructure, exploitation of flaws in Control Web Panel (e.g., CVE-2021-45467), and SSH adversary-in-the-middle (AitM) attacks.
The threat actors have also been observed using fake or stolen identities to cover their tracks, not to mention compromising infrastructure used by other perpetrators with the malware in order to meet their goals and confuse attribution efforts.
“An example is the compromise of servers responsible for collecting data from Vidar Stealer,” ESET said. “Ebury actors used the stolen identities obtained through Vidar Stealer for renting server infrastructure and in their activities, sending law enforcement bodies in the wrong directions.”
In another instance, Ebury is said to have been used to breach one of the Mirai botnet author’s systems and steal the code much before it was made public.
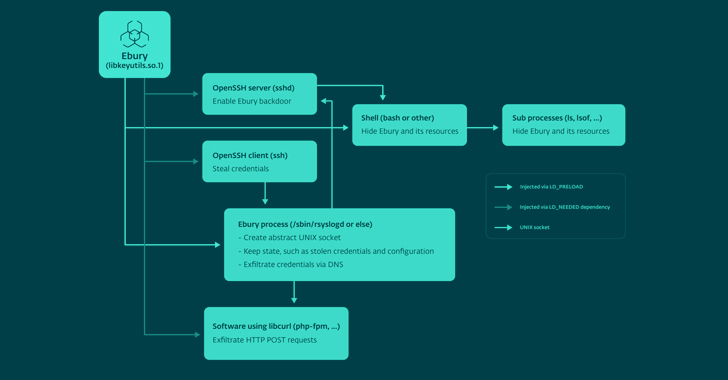
The malware acts both as a backdoor inside the OpenSSH daemon and a credential stealer, offering attackers the ability to deploy additional payloads like HelimodSteal, HelimodRedirect, and HelimodProxy, and expand their presence within a compromised network. The latest version of Ebury known to date is 1.8.2.
The updated Ebury artifacts introduce new obfuscation techniques, a domain generation algorithm (DGA), and better conceal its presence by functioning as a userland rootkit when injected inside the shell of SSH sessions.
“Those tools have the common goal of monetizing, through various methods, the servers they compromise,” ESET said. “The way servers are monetized range from credit card information theft and cryptocurrency stealing to traffic redirection, spam sending, and credential stealing.”
HelimodSteal, HelimodRedirect, and HelimodProxy are all Apache HTTP server modules used for intercepting HTTP POST requests made to the web server, redirecting HTTP requests to ads, and proxying traffic to send spam. Another new tool employed is a kernel module called KernelRedirect that implements a Netfilter hook to modify HTTP traffic to perform redirection.
Also utilized are software to hide and allow malicious traffic through the firewall, as well as Perl scripts to carry out large-scale AitM attacks within hosting providers’ data centers to breach valuable targets and steal cryptocurrency from wallets hosted on those servers.
As many as 200 servers across more than 75 networks in 34 different countries are believed to have been targeted in this manner between February 2022 and May 2023.
HelimodSteal is also designed to capture credit card data that’s submitted by a victim to an online store, effectively as a server-side web skimmer to extract the information received by the infected server.
In an alternate chain of events, the financial details can be obtained by means of Ebury or FrizzySteal, a malicious shared library that’s injected into libcurl and can exfiltrate requests made by the compromised server to external HTTP servers, such as a payment processor.
“Since both are operating within the web server or application, end-to-end encryption (HTTPS) cannot protect against this threat,” ESET noted.
“Access to servers used for shared hosting grants them access to a lot of unencrypted web traffic, which they leverage for stealthy redirection or capturing details submitted in online forms.”
Found this article interesting? Follow us on Twitter and LinkedIn to read more exclusive content we post.