In the first step of your doxxing research, we collected a list of our online footprint, digging out the most important accounts that you want to protect and obsolete or forgotten accounts you no longer use. Because the most recent and relevant data is likely to live in the accounts you use regularly, our next step will be to review the full scope of what’s visible from these accounts and to set more intentional boundaries on what is shared.
It’s important to note here that the goal isn’t to eliminate every trace of yourself from the internet and never go online again. That’s not realistic for the vast majority of people in our connected world (and I don’t know about you, but even if it was I wouldn’t want to!) And whether it’s planning for an individual or a giant organization, security built to an impossible standard is destined to fail. Instead, we are shifting you from default to intentional sharing, and improving visibility and control over what you do want to share.
LOCKING THE FRONT DOOR
Before making changes to the settings and permissions for each of these accounts, we’re going to make sure that access to the account itself is secure. You can start with your email accounts (especially any that you use as a recovery email for forgotten passwords, or use for financial, medical, or other sensitive communications). This shouldn’t take very long for each site, and involves a few straightforward steps:
Set a long, unique password for each account. Weak or reused passwords are most vulnerable to attack, and as you most likely discovered during your HaveIBeenPwned search, the odds are better than not that you found your username or email in at least one previous breach.
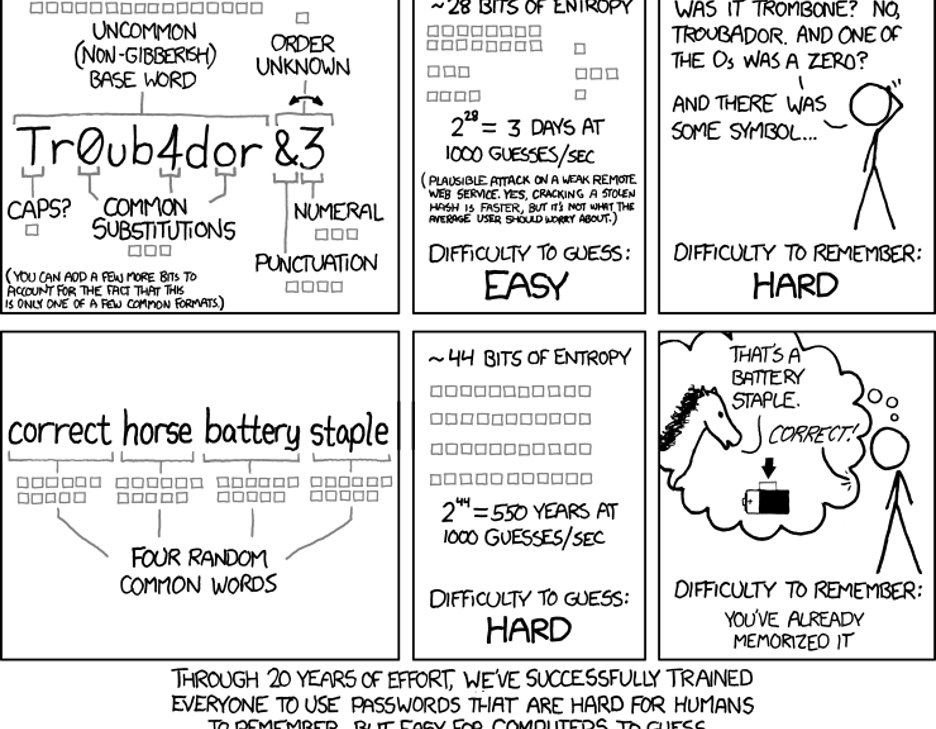
The best way to prevent a breached password from exposing another account to attack is to use a unique password for for every website you visit. And while you may have heard previous advice on strong passwords (along the lines of “eight or more characters, with a mix of upper/lower case letters, numbers, and special characters”), more recent standards emphasize the importance of longer passwords. For a great explanation of why longer passwords work better than shorter, multi-character type passwords, check out this excellent XKCD strip:
A password manager will make this process much easier, as most have the ability to generate unique passwords and allow you to tailor their length and complexity. While we’re on the topic of what makes a good password, make sure that the password to access your password manager is both long and memorable.
You don’t want to save or auto-fill that password because it acts as the “keys to the kingdom” for everything else, so I recommend following a process like the one outlined in the comic above, or another mnemonic device, to help you remember that password. Once you’ve reset the password, check for a “log out of active devices” option to make sure the new password is used.
Set up strong authentication using multi-factor authentication wherever it is supported. Whether short or long, a password on its own is still vulnerable to capture or compromise. One way experts have improved login security is through the use of multi-factor authentication. Multi-factor authentication is often shortened to MFA and can also be referred to as two-step authentication or 2FA.
MFA uses two or more “factors” verifying something you know, something you have, or something you are. A password is an example of “something you know”, and here are a few of the most common methods used for an additional layer of security:
Email/SMS passcodes: This has become a common method for verifying logins to secure services like bank accounts and health portals. You enter your username and password and are prompted to enter a short code that is sent to your email or cell number associated with the account. It’s a popular method because it requires no additional setup. However, it suffers from the same weaknesses email accounts and phone numbers do on their own: If you set up 2FA for a social media service using email passcodes on an email using only a password for access, you’re effectively back to the security of a password alone. This is better than nothing, but if one of the other factors is supported you should likely opt for it instead.
Hardware/software passcode generators: This method uses either a physical device like a keyfob or USB dongle or an installed soft token generator app on a smart device to generate a short code like those sent to SMS or email without relying on those channels. You may use an app tied to the service (like the Steam Authenticator on the iOS/Android Steam app) or scan a QR code to store the new account in a third-party authenticator app like Google Authenticator or Duo Mobile. This still isn’t ideal, because you’re typing in your passcode on the same device where you entered your password – meaning if someone is able to intercept or trick you into revealing your password, they may very well be able to do the same with the passcode.
On-device prompt: Rather than using a trusted email or phone number to verify it’s you, this method uses a trusted device (something you have) to confirm your login. If you’ve tried logging into a Gmail account and been prompted to approve your login through another already-approved device, you’re completing an on-device prompt. Another type of on-device prompt would be login approvals sent through push notifications to an authenticator app like Duo Mobile, which will provide you with other details about the login to your account. Because you approve this prompt on a separate device (your phone) than the device used to log in (your computer), this is more resistant to being intercepted or captured than a passcode generator.
Biometric authentication: If you buy an app on the Google Play Store or iOS App Store, you may be prompted to confirm your purchase with a fingerprint sensor or facial recognition instead of entering a password. The shift to unlocking our mobile devices through biometric methods (unique physical measurements or “something you are”) has opened up a more convenient strong authentication. This same method can be used as a prompt on its own, or as a requirement to approve an on-device prompt.
If you want to know more about the different ways you can log in with strong authentication and how they vary in effectiveness, check out the Google Security Team blog post “Understanding the Root Cause of Account Takeover.”
PASSWORD QUESTIONS: WHERE DID YOUR FIRST PET GO TO HIGH SCHOOL?
Before we move on from passwords and 2FA, I want to highlight a second step to log in that doesn’t meet the standard of strong authentication: password questions. These are usually either a secondary prompt after entering username and password, or used to verify your identity before sending a password reset link. The problem is that many of the most commonly-used questions rely on semi-public information and, like passcodes, are entered on the same device used to log in.
Another common practice is leveraging common social media quizzes/questionnaires that people post on their social media account. If you’ve seen your friends post their “stage name” by taking the name of their first pet and the street they grew up on, you may notice that’s a combination of two pretty common password questions! While not a very targeted or precise method of attack, the casual sharing of these surveys can have consequences beyond their momentary diversion.
One of the first widely-publicized doxxings happened when Paris Hilton’s contact list, notes, and photos were accessed by resetting her password using the password question, “what is your favorite pet’s name?”. Because Hilton had previously discussed her beloved chihuahua, Tinkerbell, the attacker was able to use this information to access the account.
Sometimes, though, you’ll be required to use these password questions, and in those cases I’ve got a simple rule to keep you safe: lie! That’s right, you won’t be punished if you fib when entering the answers to your password questions so that the answers can’t be researched, and most password managers also include a secure note field that will let you save your questions and answers in case you need to recall them later.
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels