The threat actors behind an ongoing malware campaign targeting software developers have demonstrated new malware and tactics, expanding their focus to include Windows, Linux, and macOS systems.
The activity cluster, dubbed DEV#POPPER and linked to North Korea, has been found to have singled out victims across South Korea, North America, Europe, and the Middle East.
“This form of attack is an advanced form of social engineering, designed to manipulate individuals into divulging confidential information or performing actions that they might normally not,” Securonix researchers Den Iuzvyk and Tim Peck said in a new report shared with The Hacker News.
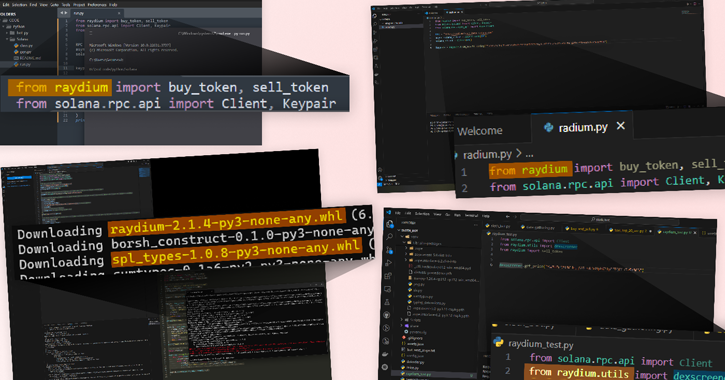
DEV#POPPER is the moniker assigned to an active malware campaign that tricks software developers into downloading booby-trapped software hosted on GitHub under the guise of a job interview. It shares overlaps with a campaign tracked by Palo Alto Networks Unit 42 under the name Contagious Interview.
Signs that the campaign was broader and cross-platform in scope emerged earlier this month when researchers uncovered artifacts targeting both Windows and macOS that delivered an updated version of a malware called BeaverTail.
The attack chain document by Securonix is more or less consistent in that the threat actors pose as interviewers for a developer position and urge the candidates to download a ZIP archive file for a coding assignment.
Present with the archive is an npm module that, once installed, triggers the execution of an obfuscated JavaScript (i.e., BeaverTail) that determines the operating system on which it’s running and establishes contact with a remote server to exfiltrate data of interest.
It’s also capable of downloading next-stage payloads, including a Python backdoor referred to as InvisibleFerret, which is designed to gather detailed system metadata, access cookies stored in web browsers, execute commands, upload/download files, as well as log keystrokes and clipboard content.
New features added to the recent samples include the use of enhanced obfuscation, AnyDesk remote monitoring and management (RMM) software for persistence, and improvements to the FTP mechanism employed for data exfiltration.
Furthermore, the Python script acts as a conduit to run an ancillary script that’s responsible for stealing sensitive information from various web browsers – Google Chrome, Opera, and Brave – across different operating systems.
“This sophisticated extension to the original DEV#POPPER campaign continues to leverage Python scripts to execute a multi-stage attack focused on exfiltrating sensitive information from victims, though now with much more robust capabilities,” the researchers said.
Found this article interesting? Follow us on Twitter and LinkedIn to read more exclusive content we post.