A hacktivist group known as Head Mare has been linked to cyber attacks that exclusively target organizations located in Russia and Belarus.
“Head Mare uses more up-to-date methods for obtaining initial access,” Kaspersky said in a Monday analysis of the group’s tactics and tools.
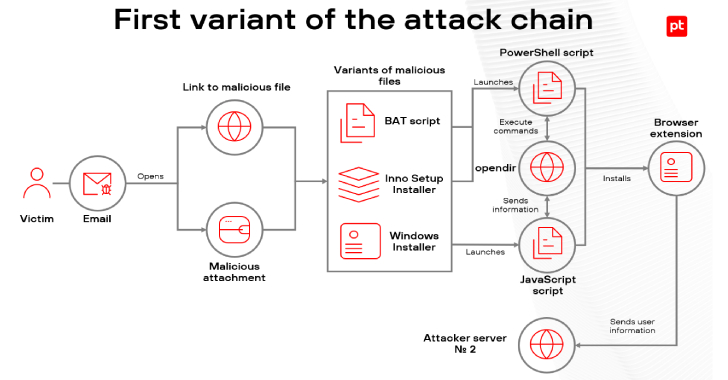
“For instance, the attackers took advantage of the relatively recent CVE-2023-38831 vulnerability in WinRAR, which allows the attacker to execute arbitrary code on the system via a specially prepared archive. This approach allows the group to deliver and disguise the malicious payload more effectively.”
Head Mare, active since 2023, is one of the hacktivist groups attacking Russian organizations in the context of the Russo-Ukrainian conflict that began a year before.
It also maintains a presence on X, where it has leaked sensitive information and internal documentation from victims. Targets of the group’s attacks include governments, transportation, energy, manufacturing, and environment sectors.
Unlike other hacktivist personas that likely operate with an aim to inflict “maximum damage” to companies in the two countries, Head Mare also encrypts victims’ devices using LockBit for Windows and Babuk for Linux (ESXi), and demands a ransom for data decryption.
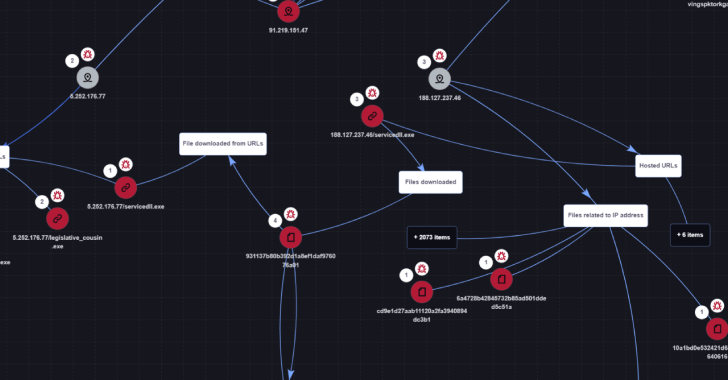
Also part of its toolkit are PhantomDL and PhantomCore, the former of which is a Go-based backdoor that’s capable of delivering additional payloads and uploading files of interest to a command-and-control (C2) server.
PhantomCore (aka PhantomRAT), a predecessor to PhantomDL, is a remote access trojan with similar features, allowing for downloading files from the C2 server, uploading files from a compromised host to the C2 server, as well as executing commands in the cmd.exe command line interpreter.
“The attackers create scheduled tasks and registry values named MicrosoftUpdateCore and MicrosoftUpdateCoree to disguise their activity as tasks related to Microsoft software,” Kaspersky said.
“We also found that some LockBit samples used by the group had the following names: OneDrive.exe [and] VLC.exe. These samples were located in the C:ProgramData directory, disguising themselves as legitimate OneDrive and VLC applications.”
Both the artifacts have been found to be distributed via phishing campaigns in the form of business documents with double extensions (e.g., решение №201-5_10вэ_001-24 к пив экран-сои-2.pdf.exe or тз на разработку.pdf.exe).
Another crucial component of its attack arsenal is Sliver, an open-source C2 framework, and a collection of various publicly available tools such as rsockstun, ngrok, and Mimikatz that facilitate discovery, lateral movement, and credential harvesting.
The intrusions culminate in the deployment of either LockBit or Babuk depending on the target environment, followed by dropping a ransom note that demands a payment in exchange for a decryptor to unlock the files.
“The tactics, methods, procedures, and tools used by the Head Mare group are generally similar to those of other groups associated with clusters targeting organizations in Russia and Belarus within the context of the Russo-Ukrainian conflict,” the Russian cybersecurity vendor said.
“However, the group distinguishes itself by using custom-made malware such as PhantomDL and PhantomCore, as well as exploiting a relatively new vulnerability, CVE-2023-38831, to infiltrate the infrastructure of their victims in phishing campaigns.”
Found this article interesting? Follow us on Twitter and LinkedIn to read more exclusive content we post.