A hacktivist group known as Twelve has been observed using an arsenal of publicly available tools to conduct destructive cyber attacks against Russian targets.
“Rather than demand a ransom for decrypting data, Twelve prefers to encrypt victims’ data and then destroy their infrastructure with a wiper to prevent recovery,” Kaspersky said in a Friday analysis.
“The approach is indicative of a desire to cause maximum damage to target organizations without deriving direct financial benefit.”
The hacking group, believed to have been formed in April 2023 following the onset of the Russo-Ukrainian war, has a track record of mounting cyber attacks that aim to cripple victim networks and disrupt business operations.
It has also been observed conducting hack-and-leak operations that exfiltrate sensitive information, which is then shared on its Telegram channel.
Kaspersky said Twelve shares infrastructural and tactical overlaps with a ransomware group called DARKSTAR (aka COMET or Shadow), raising the possibility that the two intrusion sets are likely related to one another or part of the same activity cluster.
“At the same time, whereas Twelve’s actions are clearly hacktivist in nature, DARKSTAR sticks to the classic double extortion pattern,” the Russian cybersecurity vendor said. “This variation of objectives within the syndicate underscores the complexity and diversity of modern cyberthreats.”
The attack chains start with gaining initial access by abusing valid local or domain accounts, after which the Remote Desktop Protocol (RDP) is used to facilitate lateral movement. Some of these attacks are also carried out via the victim’s contractors.
“To do this, they gained access to the contractor’s infrastructure and then used its certificate to connect to its customer’s VPN,” Kaspersky noted. “Having obtained access to that, the adversary can connect to the customer’s systems via the Remote Desktop Protocol (RDP) and then penetrate the customer’s infrastructure.”
Prominent among the other tools used by Twelve are Cobalt Strike, Mimikatz, Chisel, BloodHound, PowerView, adPEAS, CrackMapExec, Advanced IP Scanner, and PsExec for credential theft, discovery, network mapping, and privilege escalation. The malicious RDP connections to the system are tunneled through ngrok.
Also deployed are PHP web shells with capabilities to execute arbitrary commands, move files, or send emails. These programs, such as the WSO web shell, are readily available on GitHub.
In one incident investigated by Kaspersky, the threat actors are said to have exploited known security vulnerabilities (e.g., CVE-2021-21972 and CVE-2021-22005) in VMware vCenter to deliver a web shell that then was used to drop a backdoor dubbed FaceFish.
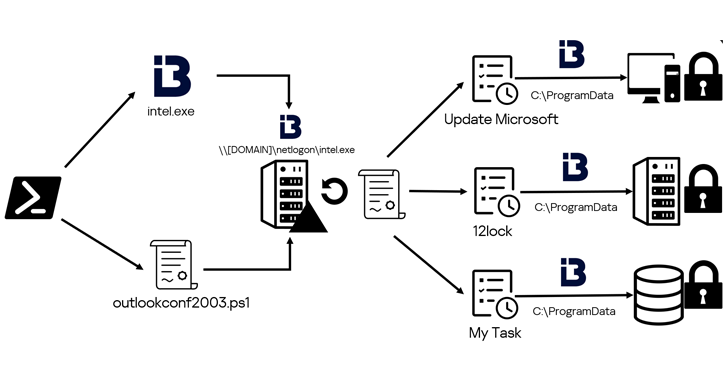
“To gain a foothold in the domain infrastructure, the adversary used PowerShell to add domain users and groups, and to modify ACLs (Access Control Lists) for Active Directory objects,” it said. “To avoid detection, the attackers disguised their malware and tasks under the names of existing products or services.”
Some of the names used include “Update Microsoft,” “Yandex,” “YandexUpdate,” and “intel.exe.”
The attacks are also characterized by the use of a PowerShell script (“Sophos_kill_local.ps1”) to terminate processes related to Sophos security software on the compromised host.
The concluding stages entail using the Windows Task Scheduler to launch ransomware and wiper payloads, but not before gathering and exfiltrating sensitive information about their victims via a file-sharing service called DropMeFiles in the form of ZIP archives.
“The attackers used a version of the popular LockBit 3.0 ransomware, compiled from publicly available source code, to encrypt the data,” Kaspersky researchers said. “Before starting work, the ransomware terminates processes that may interfere with the encryption of individual files.”
The wiper, identical to the Shamoon malware, rewrites the master boot record (MBR) on connected drives and overwrites all file contents with randomly generated bytes, effectively preventing system recovery.
“The group sticks to a publicly available and familiar arsenal of malware tools, which suggests it makes none of its own,” Kaspersky noted. “This makes it possible to detect and prevent Twelve’s attacks in due time.”
Found this article interesting? Follow us on Twitter and LinkedIn to read more exclusive content we post.