Government entities in the Middle East have been targeted as part of a previously undocumented campaign to deliver a new backdoor dubbed CR4T.
Russian cybersecurity company Kaspersky said it discovered the activity in February 2024, with evidence suggesting that it may have been active since at least a year prior. The campaign has been codenamed DuneQuixote.
“The group behind the campaign took steps to prevent collection and analysis of its implants and implemented practical and well-designed evasion methods both in network communications and in the malware code,” Kaspersky said.
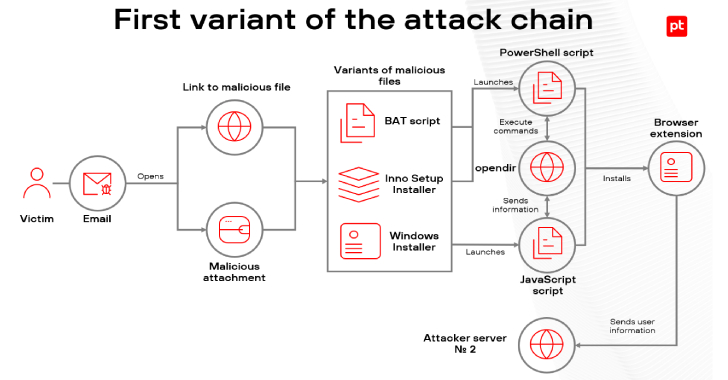
The starting point of the attack is a dropper, which comes in two variants — a regular dropper that’s either implemented as an executable or a DLL file and a tampered installer file for a legitimate tool named Total Commander.
Regardless of the method used, the primary function of the dropper is to extract an embedded command-and-control (C2) address that’s decrypted using a novel technique to prevent the server address from being exposed to automated malware analysis tools.
Specifically, it entails obtaining the filename of the dropper and stringing it together with one of the many hard-coded snippets from Spanish poems present in the dropper code. The malware then calculates the MD5 hash of the combined string, which acts as the key to decode the C2 server address.
The dropper subsequently establishes connections with the C2 server and downloads a next-stage payload after providing a hard-coded ID as the User-Agent string in the HTTP request.
“The payload remains inaccessible for download unless the correct user agent is provided,” Kaspersky said. “Furthermore, it appears that the payload may only be downloaded once per victim or is only available for a brief period following the release of a malware sample into the wild.”
The trojanized Total Commander installer, on the other hand, carries a few differences despite retaining the main functionality of the original dropper.
It does away with the Spanish poem strings and implements additional anti-analysis checks that prevent a connection to the C2 server should the system have a debugger or a monitoring tool installed, the position of the cursor does not change after a certain time, the amount of RAM available is less than 8 GB, and the disk capacity is less than 40 GB.
CR4T (“CR4T.pdb”) is a C/C++-based memory-only implant that grants attackers access to a console for command line execution on the infected machine, performs file operations, and uploads and downloads files after contacting the C2 server.
Kaspersky said it also unearthed a Golang version of CR4T with identical features, in addition to possessing the ability to execute arbitrary commands and create scheduled tasks using the Go-ole library.
On top of that, the Golang CR4T backdoor is equipped to achieve persistence by utilizing the COM objects hijacking technique and leverage the Telegram API for C2 communications.
The presence of the Golang variant is an indication that the unidentified threat actors behind DuneQuixote are actively refining their tradecraft with cross-platform malware.
“The ‘DuneQuixote’ campaign targets entities in the Middle East with an interesting array of tools designed for stealth and persistence,” Kaspersky said.
“Through the deployment of memory-only implants and droppers masquerading as legitimate software, mimicking the Total Commander installer, the attackers demonstrate above average evasion capabilities and techniques.”
Found this article interesting? Follow us on Twitter and LinkedIn to read more exclusive content we post.