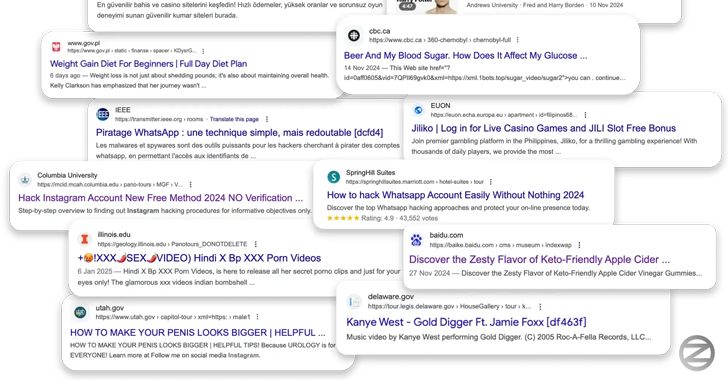
A cross-site scripting (XSS) vulnerability in a virtual tour framework has been weaponized by malicious actors to inject malicious scripts across hundreds of websites with the goal of manipulating search results and fueling a spam ads campaign at scale.
Security researcher Oleg Zaytsev, in a report shared with The Hacker News, said the campaign – dubbed 360XSS – affected over 350 websites,