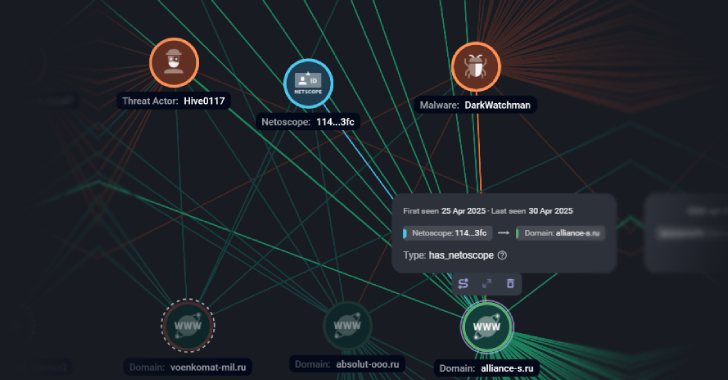
Russian companies have been targeted as part of a large-scale phishing campaign that’s designed to deliver a known malware called DarkWatchman.
Targets of the attacks include entities in the media, tourism, finance and insurance, manufacturing, retail, energy, telecom, transport, and biotechnology sectors, Russian cybersecurity company F6 said.
The activity is assessed to be the work of a