Cybersecurity researchers have discovered a new phishing campaign that spreads a new fileless variant of known commercial malware called Remcos RAT.
Remcos RAT “provides purchases with a wide range of advanced features to remotely control computers belonging to the buyer,” Fortinet FortiGuard Labs researcher Xiaopeng Zhang said in an analysis published last week.
“However, threat actors have abused Remcos to collect sensitive information from victims and remotely control their computers to perform further malicious acts.”
The starting point of the attack is a phishing email that uses purchase order-themed lures to convince recipients to open a Microsoft Excel attachment.
The malicious Excel document is designed to exploit a known remote code execution flaw in Office (CVE-2017-0199, CVSS score: 7.8) to download an HTML Application (HTA) file (“cookienetbookinetcahce.hta”) from a remote server (“192.3.220[.]22”) and launch it using mshta.exe.
The HTA file, for its part, is wrapped in multiple layers of JavaScript, Visual Basic Script, and PowerShell code to evade detection. Its main responsibility is to retrieve an executable file from the same server and execute it.
The binary subsequently proceeds to run another obfuscated PowerShell program, while also adopting an array of anti-analysis and anti-debugging techniques to complicate detection efforts. In the next step, the malicious code leverages process hollowing to ultimately download and run Remcos RAT.
“Rather than saving the Remcos file into a local file and running it, it directly deploys Remcos in the current process’s memory,” Zhang said. “In other words, it is a fileless variant of Remcos.”
Remcos RAT is equipped to harvest various kinds of information from the compromised host, including system metadata, and can execute instructions remotely issued by the attacker through a command-and-control (C2) server.
These commands allow the program to harvest files, enumerate and terminate processes, manage system services, edit Windows Registry, execute commands and scripts, capture clipboard content, alter a victim’s desktop wallpaper, enable camera and microphone, download additional payloads, record the screen, and even disable keyboard or mouse input.
The disclosure comes as Wallarm revealed that threat actors are abusing Docusign APIs to send fake invoices that appear authentic in an attempt to deceive unsuspecting users and conduct phishing campaigns at scale.
The attack entails creating a legitimate, paid Docusign account that enables the attackers to change templates and use the API directly. The accounts are then used to create specially crafted invoice templates mimicking requests to e-sign documents from well-known brands like Norton Antivirus.
“Unlike traditional phishing scams that rely on deceptively crafted emails and malicious links, these incidents use genuine DocuSign accounts and templates to impersonate reputable companies, catching users and security tools off guard,” the company said.
“If users e-sign this document, the attacker can use the signed document to request payment from the organization outside of DocuSign or send the signed document through DocuSign to the finance department for payment.”
Phishing campaigns have also been observed leveraging an unconventional tactic called ZIP file concatenation to bypass security tools and distribute remote access trojans to targets.
The method involves appending multiple ZIP archives into a single file, which introduces security issues due to the discrepancy in which different programs like 7-Zip, WinRAR, and the Windows File Explorer unpack and parse such files, thereby resulting in a scenario where malicious payloads are overlooked.
“By exploiting the different ways ZIP readers and archive managers process concatenated ZIP files, attackers can embed malware that specifically targets users of certain tools,” Perception Point noted in a recent report.
“Threat actors know these tools will often miss or overlook the malicious content hidden within concatenated archives, allowing them to deliver their payload undetected and target users who use a specific program to work with archives.”
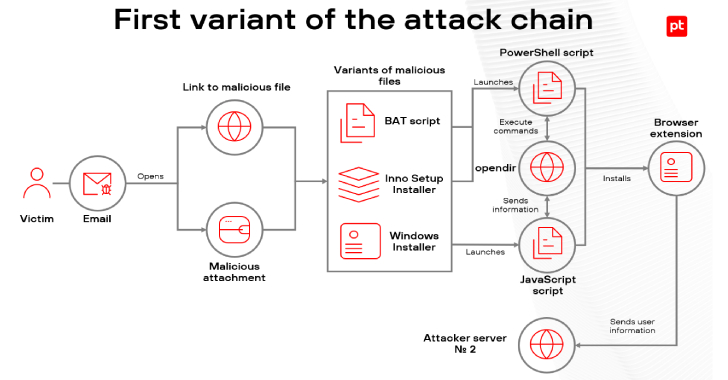
The development also comes as a threat actor known as Venture Wolf has been linked to phishing attacks targeting Russian manufacturing, construction, IT, and telecommunications sectors with MetaStealer, a fork of the RedLine Stealer malware.
Found this article interesting? Follow us on Twitter and LinkedIn to read more exclusive content we post.