A new zero-day security flaw has been discovered in Apache OfBiz, an open-source Enterprise Resource Planning (ERP) system that could be exploited to bypass authentication protections.
The vulnerability, tracked as CVE-2023-51467, resides in the login functionality and is the result of an incomplete patch for another critical vulnerability (CVE-2023-49070, CVSS score: 9.8) that was released earlier this month.
“The security measures taken to patch CVE-2023-49070 left the root issue intact and therefore the authentication bypass was still present,” the SonicWall Capture Labs threat research team, which discovered the bug, said in a statement shared with The Hacker News.
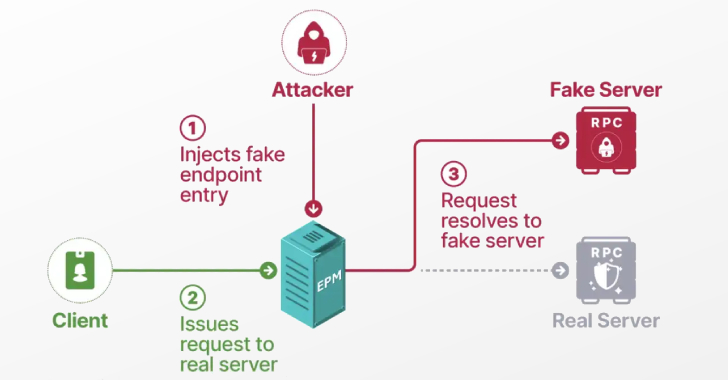
CVE-2023-49070 refers to a pre-authenticated remote code execution flaw impacting versions prior to 18.12.10 that, when successfully exploited, could allow threat actors to gain full control over the server and siphon sensitive data. It is caused due to a deprecated XML-RPC component within Apache OFBiz.
According to SonicWall, CVE-2023-51467 could be triggered using empty and invalid USERNAME and PASSWORD parameters in an HTTP request to return an authentication success message, effectively circumventing the protection and enabling a threat actor to access otherwise unauthorized internal resources.
The attack hinges on the fact that the parameter “requirePasswordChange” is set to “Y” (i.e., yes) in the URL, causing the authentication to be trivially bypassed regardless of the values passed in the username and password fields.
“The vulnerability allows attackers to bypass authentication to achieve a simple Server-Side Request Forgery (SSRF),” according to a description of the flaw on the NIST National Vulnerability Database (NVD).
Users who rely on Apache OFbiz to update to version 18.12.11 or later as soon as possible to mitigate any potential threats.
Found this article interesting? Follow us on Twitter and LinkedIn to read more exclusive content we post.