The China-linked threat actor known as Evasive Panda compromised an unnamed internet service provider (ISP) to push malicious software updates to target companies in mid-2023, highlighting a new level of sophistication associated with the group.
Evasive Panda, also known by the names Bronze Highland, Daggerfly, and StormBamboo, is a cyber espionage group that’s been active since at least 2012, leveraging backdoors such as MgBot (aka POCOSTICK) and Nightdoor (aka NetMM and Suzafk) to harvest sensitive information.
More recently, the threat actor was formally attributed to the use of a macOS malware strain called MACMA, which has been observed in the wild as far back as 2021.
“StormBamboo is a highly skilled and aggressive threat actor who compromises third-parties (in this case, an ISP) to breach intended targets,” Volexity said in a report published last week.
“The variety of malware employed in various campaigns by this threat actor indicates significant effort is invested, with actively supported payloads for not only macOS and Windows, but also network appliances.”
Public reporting from ESET and Symantec over the past two years have documented Evasive Panda’s use of MgBot and its track record of orchestrating watering hole and supply chain attacks targeting Tibetan users.
It was also found to have targeted an international non-governmental organization (NGO) in Mainland China with MgBot delivered via update channels of legitimate applications like Tencent QQ.
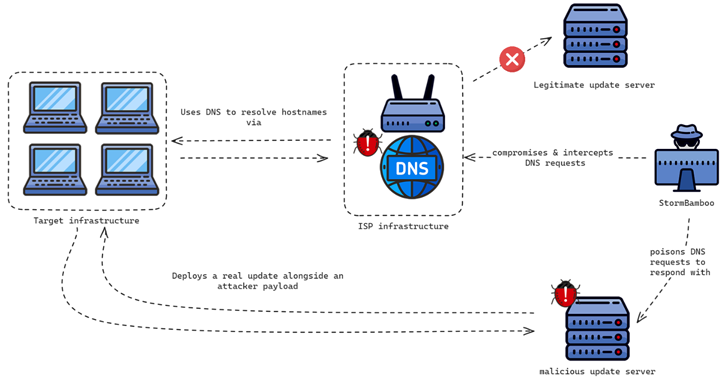
While it was speculated that the trojanized updates were either the result of a supply chain compromise of Tencent QQ’s update servers or a case of an adversary-in-the-middle (AitM) attack, Volexity’s analysis confirms it’s the latter stemming from a DNS poisoning attack at the ISP level.
Specifically, the threat actor is said to be altering DNS query responses for specific domains tied to automatic software update mechanisms, going after software that used insecure update mechanisms, such as HTTP, or did not enforce adequate integrity checks of the installers.
“It was discovered that StormBamboo poisoned DNS requests to deploy malware via an HTTP automatic update mechanism and poison responses for legitimate hostnames that were used as second-stage, command-and-control (C2) servers,” researchers Ankur Saini, Paul Rascagneres, Steven Adair, and Thomas Lancaster said.
The attack chains are fairly straightforward in that the insecure update mechanisms are abused to deliver either MgBot or MACMA depending on the operating system used. Volexity said it notified the concerned ISP to remediate the DNS poisoning attack.
One instance also entailed the deployment of a Google Chrome extension on the victim’s macOS device by modifying the Secure Preferences file. The browser add-on purports to be a tool that loads a page in compatibility mode with Internet Explorer, but its main objective is to exfiltrate browser cookies to a Google Drive account controlled by the adversary.
“The attacker can intercept DNS requests and poison them with malicious IP addresses, and then use this technique to abuse automatic update mechanisms that use HTTP rather than HTTPS,” the researchers said.
Found this article interesting? Follow us on Twitter and LinkedIn to read more exclusive content we post.