Cracked software have been observed infecting Apple macOS users with a previously undocumented stealer malware capable of harvesting system information and cryptocurrency wallet data.
Kaspersky, which identified the artifacts in the wild, said they are designed to target machines running macOS Ventura 13.6 and later, indicating the malware’s ability to infect Macs on both Intel and Apple silicon processor architectures.
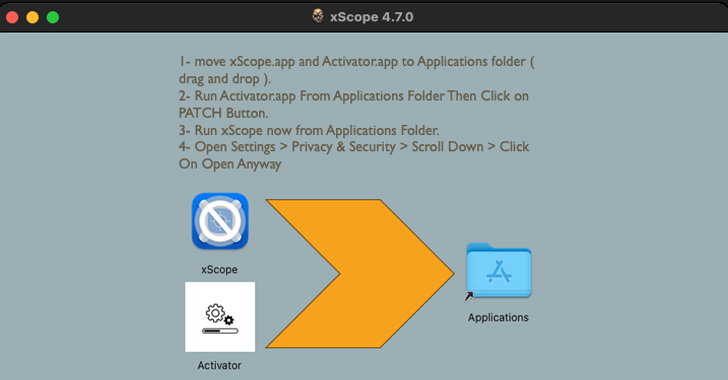
The attack chains leverage booby-trapped disk image (DMG) files that include a program named “Activator” and a pirated version of legitimate software such as xScope.
Users who end up opening the DMG files are urged to move both files to the Applications folder and run the Activator component to apply a supposed patch and run the xScope app.
Launching Activator, however, displays a prompt asking the victim to enter the system administrator password, thereby allowing it to execute a Mach-O binary with elevated permissions in order to launch the modified xScope executable.
“The trick was that the malicious actors had taken pre-cracked application versions and added a few bytes to the beginning of the executable, thus disabling it to make the user launch Activator,” security researcher Sergey Puzan said.
The next stage entails establishing contact with a command-and-control (C2) server to fetch an encrypted script. The C2 URL, for its part, is constructed by combining words from two hard-coded lists and adding a random sequence of five letters as a third-level domain name.
A DNS request for this domain is then sent to retrieve three DNS TXT records, each containing a Base64-encoded ciphertext fragment that is decrypted and assembled to construct a Python script, which, in turn, establishes persistence and functions as a downloader by reaching out to “apple-health[.]org” every 30 seconds to download and execute the main payload.
“This was a fairly interesting and unusual way of contacting a command-and-control server and hiding activity inside traffic, and it guaranteed downloading the payload, as the response message came from the DNS server,” Puzan explained, describing it as “seriously ingenious.”
The backdoor, actively maintained and updated by the threat actor, is designed to run received commands, gather system metadata, and check for the presence of Exodus and Bitcoin Core wallets on the infected host.
If found, the applications are replaced by trojanized versions downloaded from the domain “apple-analyser[.]com” that are equipped to exfiltrate the seed phrase, wallet unlock password, name, and balance to an actor-controlled server.
“The final payload was a backdoor that could run any scripts with administrator privileges, and replace Bitcoin Core and Exodus crypto wallet applications installed on the machine with infected versions that stole secret recovery phrases the moment the wallet was unlocked,” Puzan said.
The development comes as cracked software is increasingly becoming a conduit to compromise macOS users with a variety of malware, including Trojan-Proxy and ZuRu.
Found this article interesting? Follow us on Twitter and LinkedIn to read more exclusive content we post.