The Computer Emergency Response Team of Ukraine (CERT-UA) has warned of new phishing attacks that aim to infect devices with malware.
The activity has been attributed to a threat cluster it tracks as UAC-0020, which is also known as Vermin. The exact scale and scope of the attacks are presently unknown.
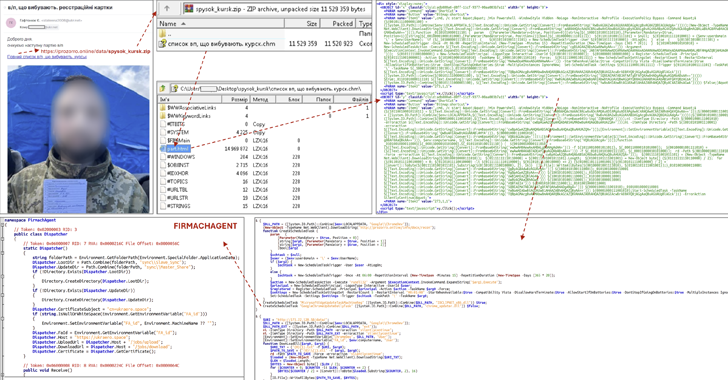
The attack chains commence with phishing messages with photos of alleged prisoners of war (PoWs) from the Kursk region, urging recipients to click on a link pointing to a ZIP archive.
The ZIP file contains a Microsoft Compiled HTML Help (CHM) file that embeds JavaScript code responsible for launching an obfuscated PowerShell script.
“Opening the file installs components of known spyware SPECTR, as well as the new malware called FIRMACHAGENT,” CERT-UA said. “The purpose of FIRMACHAGENT is to retrive the data stolen by SPECTR and send it to a remote management server.”
SPECTR is a known malware linked to Vermin as far back as 2019. The group is assessed to be linked to security agencies of the Luhansk People’s Republic (LPR).
Earlier this June, CERT-UA detailed another campaign orchestrated by the Vermin actors called SickSync that targeted defense forces in the country with SPECTR.
SPECTR is a fully-featured tool designed to harvest a wide range of information, including files, screenshots, credentials, and data from various instant messaging apps like Element, Signal, Skype, and Telegram.
Found this article interesting? Follow us on Twitter and LinkedIn to read more exclusive content we post.