Facebook users are the target of a scam e-commerce network that uses hundreds of fake websites to steal personal and financial data using brand impersonation and malvertising tricks.
Recorded Future’s Payment Fraud Intelligence team, which detected the campaign on April 17, 2024, has given it the name ERIAKOS owing to the use of the same content delivery network (CDN) oss.eriakos[.]com.
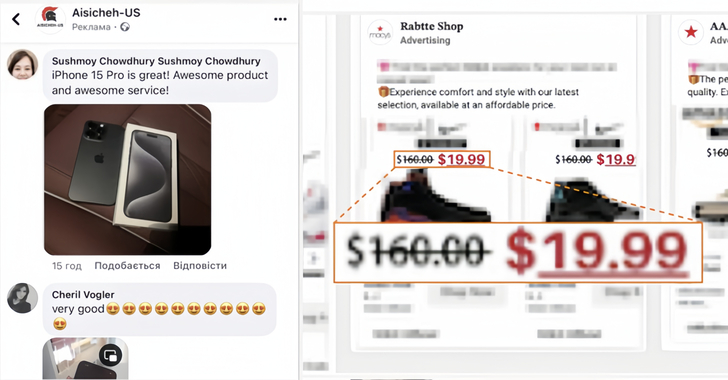
“These fraudulent sites were accessible only through mobile devices and ad lures, a tactic aimed at evading automated detection systems,” the company said, noting the network comprised 608 fraudulent websites and that the activity spans several short-lived waves.
A notable aspect of the sophisticated campaign is that it exclusively targeted mobile users who accessed the scam sites via ad lures on Facebook, some of which relied on limited-time discounts to entice users into clicking on them. Recorded Future said as many as 100 Meta Ads related to a single scam website were served in a day.
The counterfeit websites and ads have been found to mainly impersonate a major online e-commerce platform and a power tools manufacturer, as well as single out victims with bogus sales offers for products from various well-known brands. Another crucial distribution mechanism entails the use of fake user comments on Facebook to lure potential victims.
“Merchant accounts and related domains linked to the scam websites are registered in China, indicating that the threat actors operating this campaign likely established the business they use to manage the scam merchant accounts in China,” Recorded Future noted.
This is not the first time criminal e-commerce networks have sprung up with an aim to harvest credit card information and make illicit profits off fake orders. In May 2024, a massive network of 75,000 phony online stores – dubbed BogusBazaar – was discovered to have made more than $50 million by advertising shoes and apparel by well-known brands at low prices.
Then last month, Orange Cyberdefense revealed a previously undocumented traffic direction system (TDS) called R0bl0ch0n TDS that’s used to promote affiliate marketing scams through a network of fake shop and sweepstake survey sites with the goal of obtaining credit card information.
“Several distinct vectors are used for the initial dissemination of the URLs that redirect through the R0bl0ch0n TDS, indicating that these campaigns are likely carried out by different affiliates,” security researcher Simon Vernin said.
The development comes as fake Google ads displayed when searching for Google Authenticator on the search engine have been observed redirecting users to a rogue site (“chromeweb-authenticators[.]com”) that delivers a Windows executable hosted on GitHub, which ultimately drops an information stealer named DeerStealer.
What makes the ads seemingly legitimate is that they appear as if they are from “google.com” and the advertiser’s identity is verified by Google, according to Malwarebytes, which said “some unknown individual was able to impersonate Google and successfully push malware disguised as a branded Google product as well.”
Malvertising campaigns have also been spotted disseminating various other malware families such as SocGholish (aka FakeUpdates), MadMxShell, and WorkersDevBackdoor, with Malwarebytes uncovering infrastructure overlaps between the latter two, indicating that they are likely run by the same threat actors.
On top of that, ads for Angry IP Scanner have been used to lure users to fake websites, and the email address “goodgoo1ge@protonmail[.]com” has been used to register domains delivering both MadMxShell and WorkersDevBackdoor.
“Both malware payloads have the capability to collect and steal sensitive data, as well as provide a direct entry path for initial access brokers involved in ransomware deployment,” security researcher Jerome Segura said.
Found this article interesting? Follow us on Twitter and LinkedIn to read more exclusive content we post.