The Russia-linked threat actor known as Turla infected several systems belonging to an unnamed European non-governmental organization (NGO) in order to deploy a backdoor called TinyTurla-NG (TTNG).
“The attackers compromised the first system, established persistence and added exclusions to antivirus products running on these endpoints as part of their preliminary post-compromise actions,” Cisco Talos said in a new report published today.
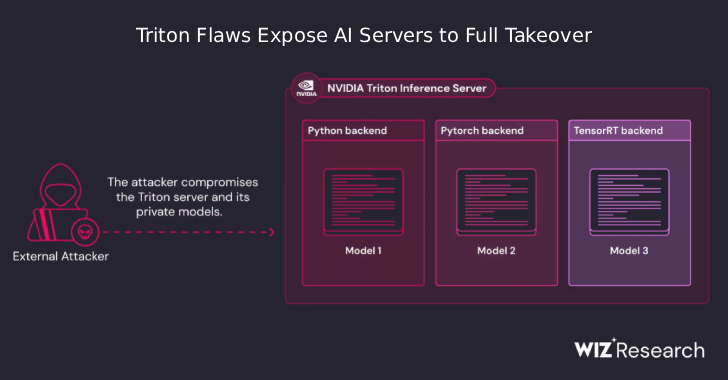
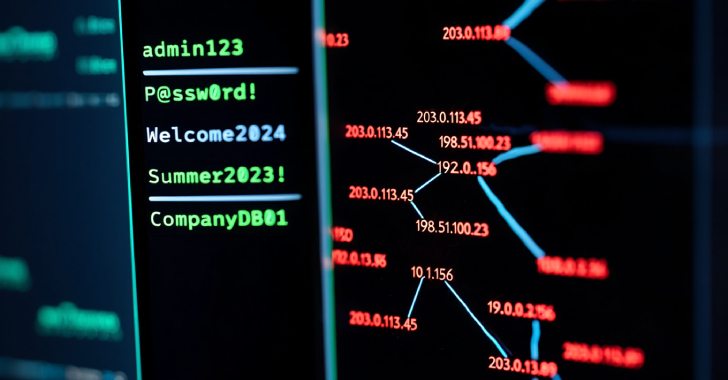
“Turla then opened additional channels of communication via Chisel for data exfiltration and to pivot to additional accessible systems in the network.”
There is evidence indicating that the infected systems were breached as early as October 2023, with Chisel deployed in December 2023 and data exfiltration taking place via the tool a month later, around January 12, 2024.
TinyTurla-NG was first documented by the cybersecurity company last month after it was found to be used in connection with a cyber attack targeting a Polish NGO working on improving Polish democracy and supporting Ukraine during the Russian invasion.
Cisco Talos told The Hacker News at the time that the campaign appears to be highly targeted and focused on a small number of organizations, most of which are located in Poland.
The attack chain involves Turla exploiting their initial access to configure Microsoft Defender antivirus exclusions to evade detection and drop TinyTurla-NG, which is then persisted by creating a malicious “sdm” service that masquerades as a “System Device Manager” service.
TinyTurla-NG acts as a backdoor to conduct follow-on reconnaissance, exfiltrate files of interest to a command-and-control (C2) server, and deploy a custom-built version of the Chisel tunneling software. The exact intrusion pathway is still being investigated.
“Once the attackers have gained access to a new box, they will repeat their activities to create Microsoft Defender exclusions, drop the malware components, and create persistence,” Talos researchers said.
Found this article interesting? Follow us on Twitter and LinkedIn to read more exclusive content we post.