The threat actors behind the PixPirate Android banking trojan are leveraging a new trick to evade detection on compromised devices and harvest sensitive information from users in Brazil.
The approach allows it to hide the malicious app’s icon from the home screen of the victim’s device, IBM said in a technical report published today.
“Thanks to this new technique, during PixPirate reconnaissance and attack phases, the victim remains oblivious to the malicious operations that this malware performs in the background,” security researcher Nir Somech said.
PixPirate, which was first documented by Cleafy in February 2023, is known for its abuse of Android’s accessibility services to covertly perform unauthorized fund transfers using the PIX instant payment platform when a targeted banking app is opened.
The constantly mutating malware is also capable of stealing victims’ online banking credentials and credit card information, as well as capturing keystrokes and intercepting SMS messages to access two-factor authentication codes.
Typically distributed via SMS and WhatsApp, the attack flow entails the use of a dropper (aka downloader) app that’s engineered to deploy the main payload (aka droppee) to pull off the financial fraud.
“Usually, the downloader is used to download and install the droppee, and from this point on, the droppee is the main actor conducting all fraudulent operations and the downloader is irrelevant,” Somech explained.
“In the case of PixPirate, the downloader is responsible not only for downloading and installing the droppee but also for running and executing it. The downloader plays an active part in the malicious activities of the droppee as they communicate with each other and send commands to execute.”
The downloader APK app, once launched, prompts the victim to update the app to either retrieve the PixPirate component from an actor-controlled server or install it if it’s embedded within itself.
What’s changed in the latest version of the droppee is the absence of activity with the action “android.intent.action.Main” and the category “android.intent.category.LAUNCHER” that allows a user to launch an app from the home screen by tapping its icon.
Put differently, the infection chain requires both the downloader and the droppee to work in tandem, with the former responsible for running the PixPirate APK by binding to a service exported by the droppee.
“Later, to maintain persistence, the droppee is also triggered to run by the different receivers that it registered,” Somech said. “The receivers are set to be activated based on different events that occur in the system and not necessarily by the downloader that initially triggered the droppee to run.”
“This technique allows the PixPirate droppee to run and hide its existence even if the victim removes the PixPirate downloader from their device.”
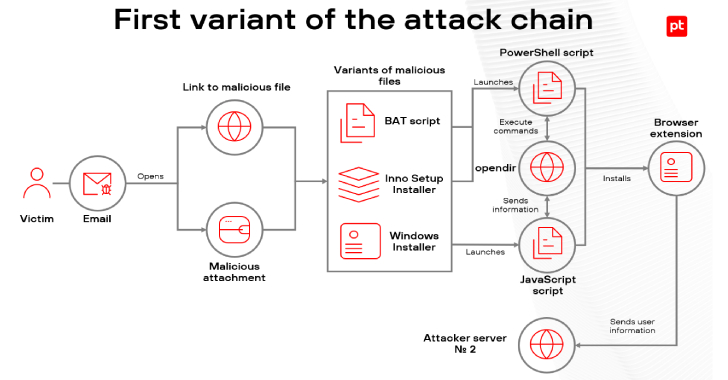
The development comes as Latin American (LATAM) banks have become the target of a new malware called Fakext that employs a rogue Microsoft Edge extension named SATiD to carry out man-in-the-browser and web injection attacks with the goal of grabbing credentials entered in the targeted bank site.
It’s worth noting that SAT ID is a service offered by Mexico’s Tax Administration Service (SAT) to generate and update electronic signatures for filing taxes online.
In select cases, Fakext is engineered to display an overlay that urges the victim to download a legitimate remote access tool by purporting to be the bank’s IT support team, ultimately enabling the threat actors to conduct financial fraud.
The campaign – active since at least November 2023 – singles out 14 banks operating in the region, a majority of which are located in Mexico. The extension has since been taken down from the Edge Add-ons store.
Found this article interesting? This article is a contributed piece from one of our valued partners. Follow us on Twitter and LinkedIn to read more exclusive content we post.