An Indian hack-for-hire group targeted the U.S., China, Myanmar, Pakistan, Kuwait, and other countries as part of a wide-ranging espionage, surveillance, and disruptive operation for over a decade.
Indian security firm under scrutiny, according to an in-depth analysis from SentinelOne, began as an educational startup offering offensive security training programs, while carrying out covert hacking operations since at least 2009.
In May 2013, ESET disclosed a set of cyber attacks targeting Pakistan with information-stealing malware. While the activity was attributed to a cluster tracked as Hangover (aka Patchwork or Zinc Emerson), evidence shows that the infrastructure was owned and controlled by the aforementioned security firm.
“The group has conducted hacking operations against high value individuals, governmental organizations, and other businesses involved in specific legal disputes,” cybersecurity company SentinelOne said in a comprehensive analysis published last week.
The Indian security firm’s “hacking operations and overall organization appear at many times informal, clumsy, and technically crude; however, their operations proved highly successful for their customers, impacting world affairs with significant success.”
The findings are based on non-public data obtained by Reuters, which called out security firm for orchestrating data theft attacks on an industrial scale against political leaders, international executives, sports figures, and others. The company, in response, has dismissed its connection with the hack-for-hire business.
“The current state of the organization significantly differs from its status a decade ago,” Tom Hegel, principal threat researcher at SentinelLabs, told The Hacker News.
“The initial entity, ‘…,’ featured in our research, no longer exists but can be regarded as the progenitor from which several present-day hack-for-hire enterprises have emerged. Factors such as rebranding, employee transitions, and the widespread dissemination of skills contribute to “…” being recognized as the pioneering group in India.”
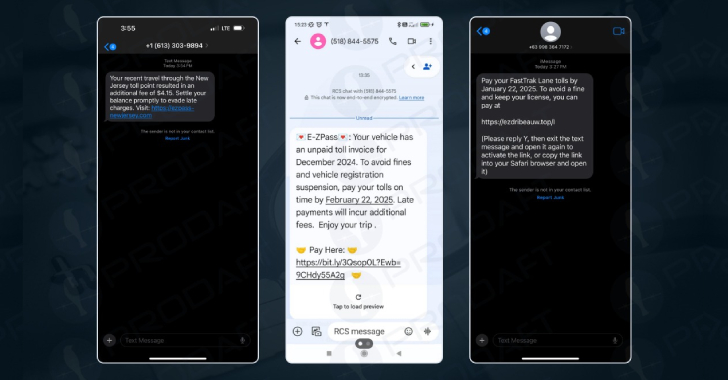
One of the core services offered by security firm was a tool named “MyCommando” (aka GoldenEye or Commando) that allowed its customers to log in to view and download campaign-specific data and status updates, communicate securely, and choose from various task options that range from open-source research to social engineering to a trojan campaign.
The targeting of China and Pakistan is confirmation that an Indian-origin mercenary group has been roped in to conduct state-sponsored attacks. It has also been identified as behind the macOS spyware known as KitM in 2013.
What’s more, SentinelOne said it also identified instances of domestic targeting with the goal of stealing login credentials of email accounts belonging to Sikhs in India and the U.S.
“In an unrelated campaign, the group also used the domain speedaccelator[.]com for an FTP server, hosting malware used in their malicious phishing emails, one of which was used on an Indian individual later targeted by the ModifiedElephant APT,” Hegel noted. It’s worth noting that Patchwork’s links to ModifiedElephant were previously identified by Secureworks.
“Operation Hangover has been confirmed as the same threat actor, evidenced by shared infrastructure and malware with “…” in the intrusion,” Hegel said. “Regarding ModifiedElephant, there’s less clarity due to only a slight overlap in time and some technical similarities.”
“Further investigation into “…” is necessary before confidently linking ModifiedElephant to the specific organization, especially considering employee and resource movements during that period. It’s crucial for industry researchers to focus on ModifiedElephant, as these activities are of significant importance but are currently not receiving sufficient attention.”
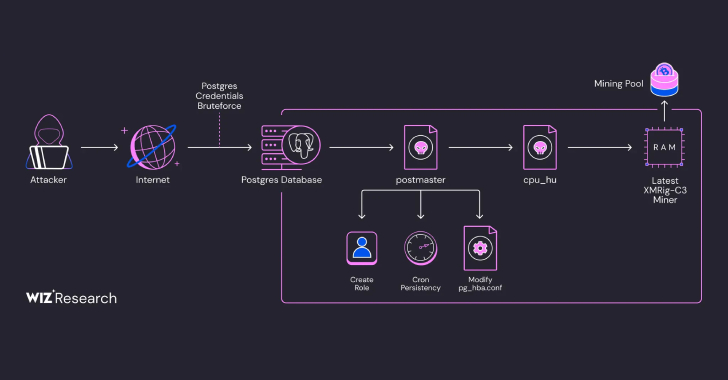
Besides leveraging a large infrastructure sourced from a third-party for data exfiltration, command-and-control (C2), phishing, and setting up decoy sites, the shadowy private-sector offensive actor (PSOA) is said to have relied on spyware and exploit services provided by private vendors like Vervata, Vupen, and Core Security.
In another noteworthy tactic, The security firm has been found leveraging a California-based freelancing platform referred to as Elance (now called Upwork) to purchase malware from external software developers, while also using its in-house employees to develop a custom collection of hacking tools.
“The research findings underscore the group’s remarkable tenacity and a proven track record of successfully executing attacks on behalf of a diverse clientele,” Hegel said.
The development comes as Aviram Azari, an Israeli private investigator, was sentenced in the U.S. to nearly seven years in federal prison on charges of computer intrusion, wire fraud, and aggravated identity theft in connection with a global hack-for-hire scheme between November 2014 to September 2019. Azari was arrested in September 2019.
“Azari owned and operated an Israeli intelligence firm,” the Department of Justice (DoJ) said last week. “Clients hired Azari to manage ‘Projects’ that were described as intelligence gathering efforts but were, in fact, hacking campaigns specifically targeting certain groups of victims.”
Aviram has also been accused of using mercenary hackers in India, a company called BellTroX Infotech (aka Amanda or Dark Basin), to help clients gain an advantage in court battles via spear-phishing attacks and ultimately gain access to victims’ accounts and steal information.
BellTrox was founded by Sumit Gupta in May 2013. Reuters disclosed in June 2022 that prior to launching the company, Gupta had worked for the aforementioned security firm.
“The hack-for-hire ecosystem will persist and expand independently of our discoveries,” Hegel said. “Nonetheless, in this exceptional situation, we possess knowledge about the organization and individuals responsible for specific targeted intrusions. Holding these attackers accountable for their actions in this case now falls within the purview of law enforcement and the affected victims.”
(The article was updated after publication to include additional comments from SentinelOne.)
Found this article interesting? Follow us on Twitter and LinkedIn to read more exclusive content we post.