Attacks included fraud, vulnerability exploitation, fake applications and info stealer deployments
- December 7, 2022
- by
- Cyber News, Cyber Threat Trends
- Less than a minute
- 465 Views
Related Post
- by CDA News Team
- May 12, 2026
The Canvas Breach Revealed A Dangerous New Reality
The Canvas Breach Revealed A Dangerous New Reality — And Most Organizations Still Aren’t Ready One breach. Massive disruption. And
- by CDA News Team
- May 6, 2026
Anthropic’s New AI Agents Aren’t Assisting Bankers Anymore.
Anthropic’s New AI Agents Aren’t Assisting Bankers Anymore. They’re Replacing Them. Built for Wall Street, they are designed to execute—not
- by Robert Gorman
- May 4, 2026
AI Just Found Thousands of Weak Spots in
The next bank breach won’t come from a new hack. It will come from a flaw that’s been sitting there
- by CDA Marketing
- March 25, 2026
CDA Achieves 8(a) Status
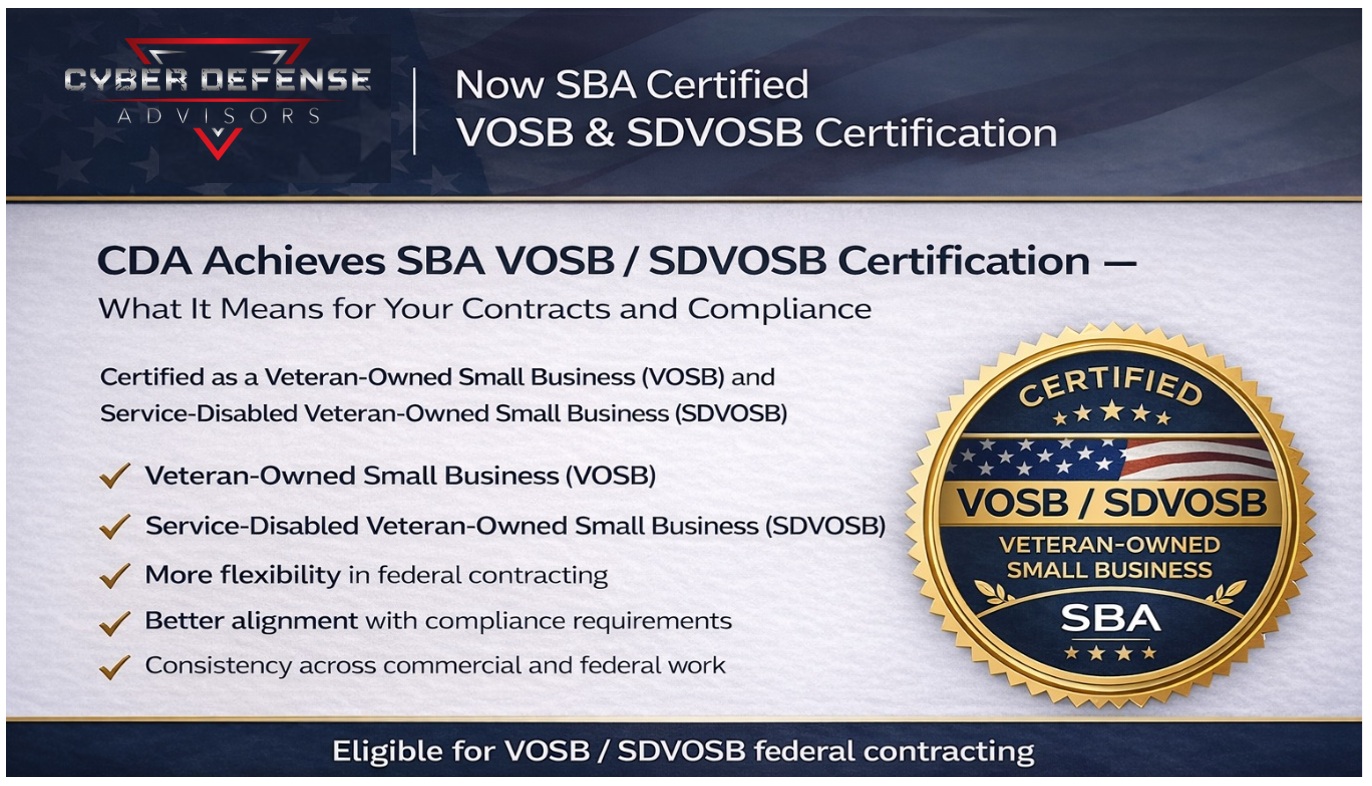
CDA Achieves SBA VOSB / SDVOSB Certification — What It Means for Your Contracts & Compliance Cyber Defense Advisors (CDA)